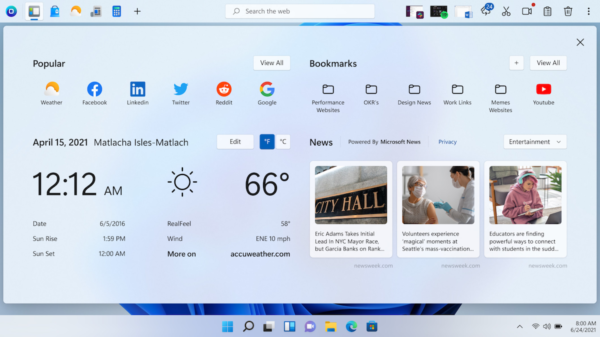
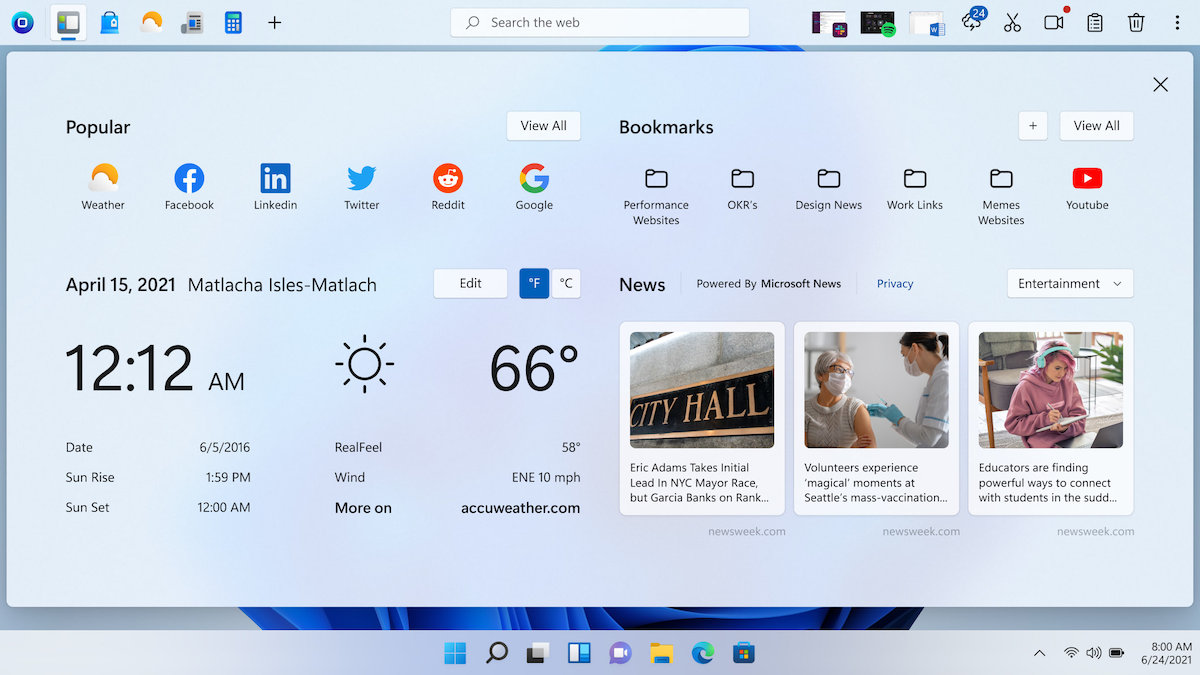
OneLaunch presents itself as a useful Windows utility, offering a customizable dock, web browser, and a suite of features. Yet, it’s often flagged as malware, sparking discussions about its true nature and safety for your device. This article peels back the layers of OneLaunch, examining why it raises concerns and offering solutions to keep your system protected.
The Murky World of Potentially Unwanted Programs (PUPs)
OneLaunch falls into the grey area of Potentially Unwanted Programs. Unlike traditional malware designed for sabotage, PUPs don’t directly inflict harm but degrade your user experience in undesirable ways. Here’s what makes OneLaunch fall into this category:
- Sneaky Installations: The primary source of distrust towards OneLaunch stems from its tendency to hitch a ride onto your system alongside other free software downloads. Without careful scrutiny of installation screens, you might accidentally give it the green light.
- Unapproved Browser Hijacking: OneLaunch might seize control of your default search engine and homepage without clear or revocable permission, redirecting your searches for its own, often ad-driven, purposes.
- Privacy Concerns: The lack of transparency about data collection practices creates further suspicion. Users may wonder about the type of information OneLaunch gathers and its potential use.
- Ad Overload: An onslaught of intrusive advertisements can diminish your browsing experience and may even expose you to risky ad content.
- Persistent Persistence: Once established, removing all traces of OneLaunch can be tricky, sometimes requiring more than just basic uninstallation procedures.
The Line Between PUP and Malware
Understanding the nuance is critical. While OneLaunch isn’t a destructive virus, it shares common strategies with malware:
- Exploiting User Habits: Both capitalize on users who skim installation instructions, enabling unwanted programs to install unnoticed.
- Undermining User Control: Changing system settings without adequate consent demonstrates disregard for user choice.
- Potential Security Loopholes: PUPs, depending on their complexities, could become attack vectors for more severe malware down the line.
How to Remove OneLaunch Malware and Restore Control
If you find OneLaunch on your system, here’s a three-pronged approach for elimination:
- Conventional Uninstall: Start by attempting to remove it via the standard “Programs and Features” section in Windows.
- Enlist Anti-Malware Aid: If simple removal fails, employ a reputable anti-malware suite. Run a deep scan to root out and quarantine any associated files.
- Manual Cleanup: After using your anti-malware tools, double-check and reset your browser’s default search engine and homepage preferences. Vigilance helps to ensure no settings persist.
Prevention is Better Than Cure
Arm yourself with the following best practices to avert OneLaunch and similar PUP encounters:
- Practice Safe Downloading: Only get software from official websites or trusted repositories. Avoid freeware sites tempting you with a flurry of bundled offerings.
- Read the Fine Print: Pay meticulous attention during installation wizards. Deselect any checkboxes suggesting additional installs you don’t explicitly want.
- Maintain a Security Shield: Invest in a robust antivirus/anti-malware program capable of real-time monitoring and blocking emerging threats.
OneLaunch Defense: Debunking the Myths
OneLaunch has responded to the negative perceptions https://blog.onelaunch.com/what-is-onelaunch-debunked/. They point out, in many cases, antivirus products flag the installation method as the ‘issue’. Transparency on the company’s part would ease user worries and bolster their reputation.
Final Verdict
OneLaunch toes the line between useful functionality and undesired invasiveness. For cautious users, the intrusive techniques outweigh any potential benefits. By exercising caution and understanding these strategies, you safeguard your device and digital experience.
OneLaunch’s privacy policy leaves several areas open to uncertainty. While they may not explicitly intend to steal sensitive data, a lack of transparency about the information they collect could leave users vulnerable.
Follow these precautions:
- Download software exclusively from official websites or trustworthy sources.
- Examine every single step of the software installation process, deselecting unwanted add-ons.
- Keep a robust antivirus/anti-malware program active on your system.
It’s most likely OneLaunch came bundled with other free software you downloaded. These installations often sneak additional programs in if you’re not paying close attention to every selection you make during the setup process.
These might be telltale signs: * Your default search engine or homepage has changed without your permission. * Intrusive advertisements appear with unusual frequency. * You see “OneLaunch” listed in your installed programs.
A: PUPs can be persistent. Use a powerful anti-malware program for a thorough scan and quarantine any related files. You may also need to reset your browser settings manually to undo any changes OneLaunch imposed.
While not classic malware that causes direct damage, OneLaunch qualifies as a Potentially Unwanted Program (PUP). Its deceptive installation, browser hijacking, and potential privacy issues warrant concern and align with harmful software tactics.
Absolutely! Reporting potentially unwanted programs helps security companies refine their detection and protect other users. Your input contributes to a safer online ecosystem.